IoT & Edge Devices
Securing the constrained, hyper-connected world against the quantum threat.
The Internet of Things (IoT) and Edge computing networks are expanding rapidly, embedding intelligence into everything from industrial sensors to consumer appliances. However, these devices face a unique security paradox: they possess strictly limited power, memory, and physical area, yet they are deployed in the field for decades. Cryptography embedded today must be resilient against the quantum computers of tomorrow.
The Constrained Environment Challenge
Migrating to NIST-standardized Post-Quantum Cryptography (PQC) introduces significant computational overhead. Algorithms like ML-KEM and ML-DSA require larger key sizes and complex polynomial arithmetic that can easily overwhelm standard microcontrollers.
Without careful engineering, implementing PQC on the Edge can lead to:
- Unacceptable latency in secure boot processes.
- Exhaustion of available SRAM/Flash memory.
- Increased power consumption, draining battery-operated endpoints.
- Vulnerability to physical Side-Channel Attacks (SCA).

Quantum-Safe Solutions for IoT
Whether you need a pure software update for existing microcontrollers, a dedicated hardware IP core for a new ASIC, or a hybrid approach, we have the architecture to secure your endpoint.

PQSecure-SW™
Memory-Optimized Software Stack. Features our “Small Variant” deployment profile designed specifically for constrained MCUs. Includes stack-optimized C implementations, memory-safe Rust, and ARM/RISC-V assembly acceleration to minimize firmware footprint.

PQSecure-HW™
Ultra-Low Area Hardware IP. Features our “Tiny Tier” and “Compact Tier” hardware accelerators. Designed for the smallest possible silicon area with built-in side-channel protections, making it ideal for integration into secure elements and IoT System-on-Chips (SoCs).
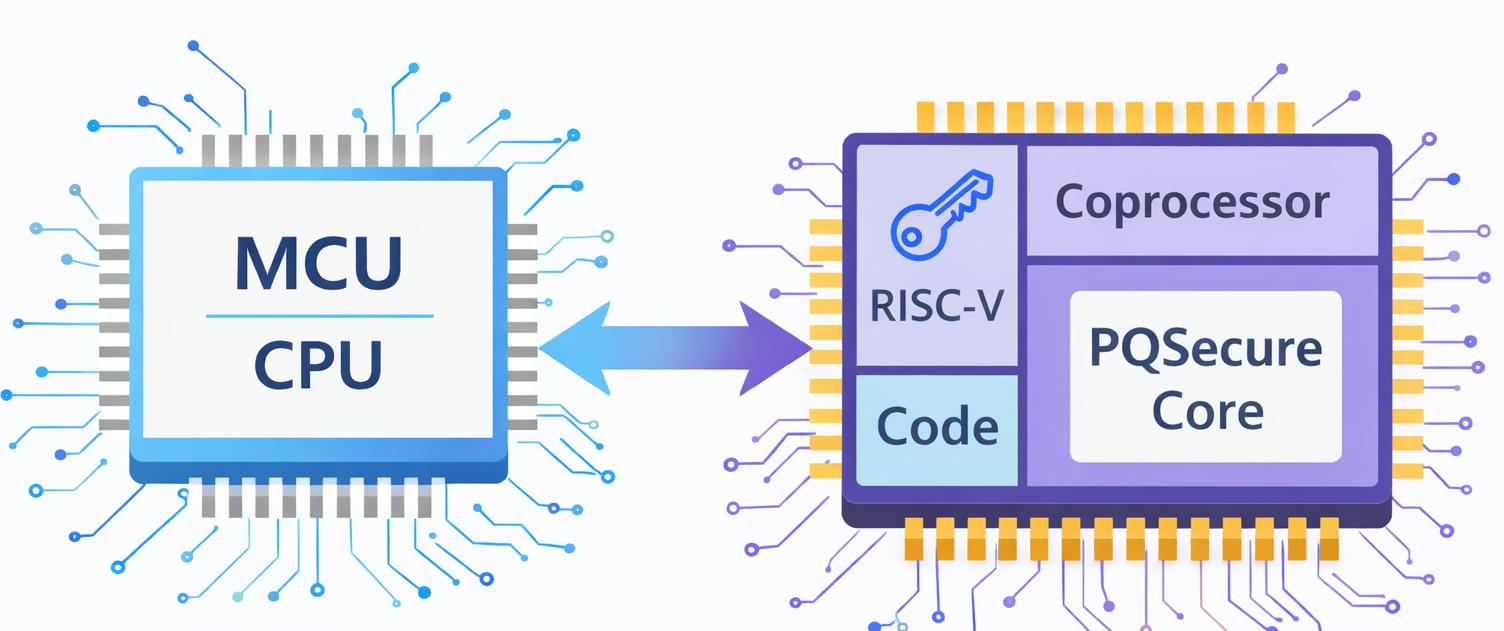
HW/SW Co-Design™
The Best of Both Worlds. Balances hardware acceleration for heavy PQC math with software-based cryptographic agility. Perfect for IoT gateways and edge nodes that require high throughput, secure boot, and the ability to receive Over-the-Air (OTA) algorithm updates.
